
Customer Access & Identity Management
Harness the power of seamless identity management with our revolutionary CIAM platform.
How does it work?
Streamline Customer Access & Identity management with Metrics Matter
Configure Organizations
Establish the organizational structure and invite colleagues to collaborate.
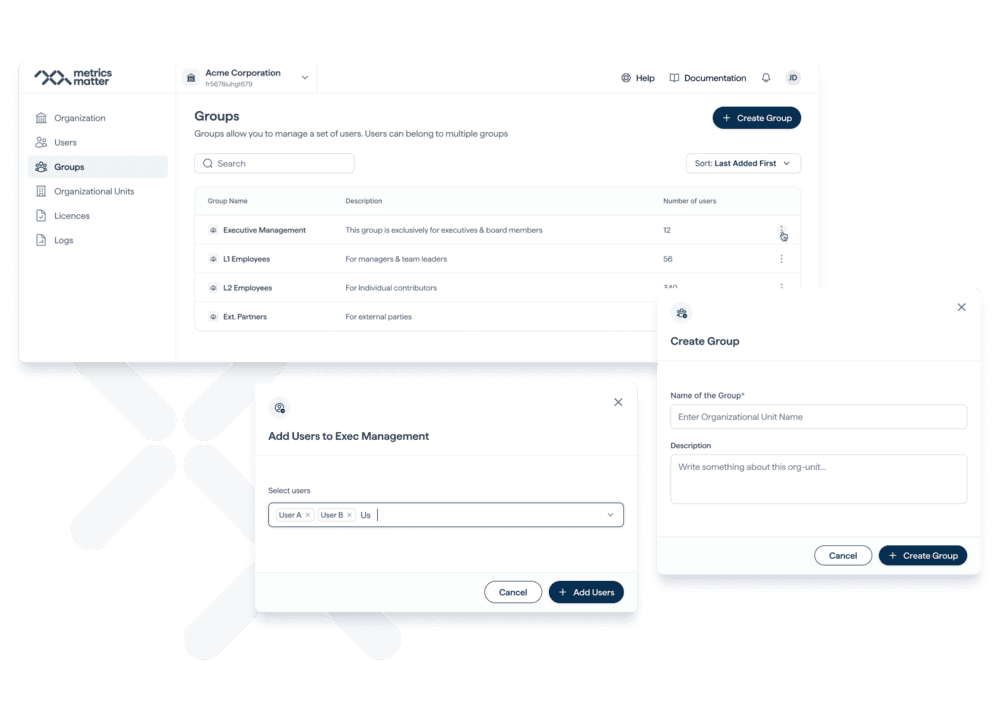
Setup Users & Groups
Securely onboard and offboard B2B users to access data through your platform.
Set Policy
Charge your customers as you like be it Subscription, One-Time or Adhoc, we’ve got you covered.
Manage
Self-serve product with engine of growth analytics to help you securely and easily onboard users, offer subscriptions and manage billing.
Centralize all operations in one place
Empower your business with a self-service solution equipped with growth analytics to effortlessly onboard users, provide subscription options, and securely streamline billing management.
Onboarding
We facilitate the onboarding of new B2B customers and organizations on your behalf through a user-friendly self-serve process that enhances conversion rates.
- Streamlined Onboarding
- Improved Conversion Rates
- Enhanced Efficiency
- Business Growth
- Customer Commitment
Identity Management
Effectively oversee the entire user identity lifecycle within your organization.
- Complete Identity Lifecycle Management
- End-to-End Control
- Enhanced Security and Compliance
- Streamlined Access
Access Management
Ensure a secure and seamless login experience by employing the suitable authorization method for your applications.
- Secure and User-Friendly Login
- Tailored Authorization Methods
- Enhanced Security and Convenience
- User Satisfaction and Engagement
- Combine different authorization methods
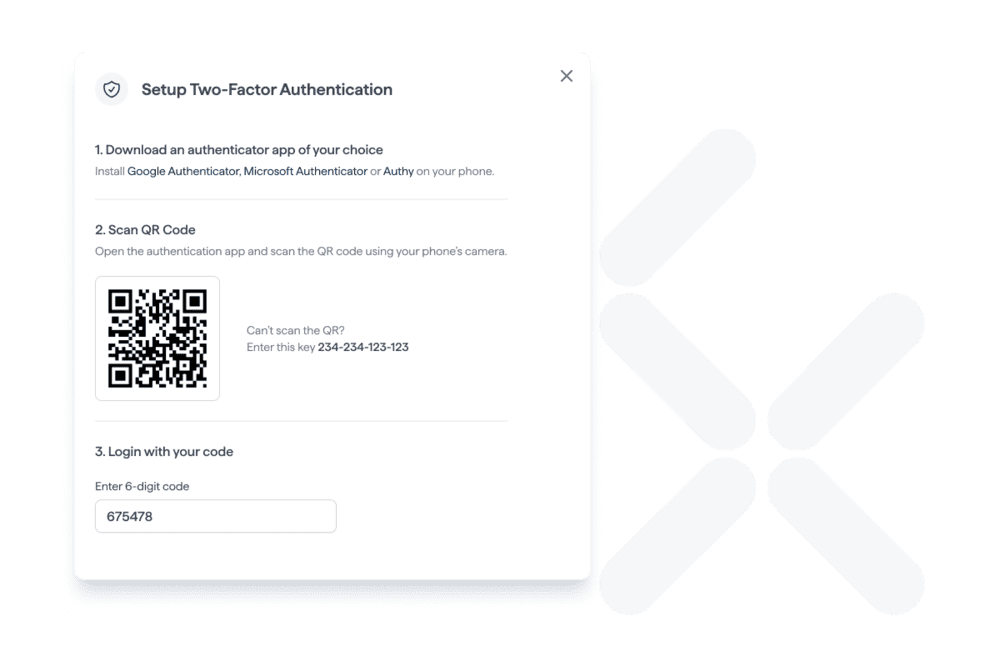
Authentication
Deliver a seamless and secure login process by enabling authentication through a variety of standard providers.
- Flexible User Login Experience
- Multiple Well-Known Providers
- Smooth and Secure Process
- User-Friendly Environment
- Positive and Secure User Experience
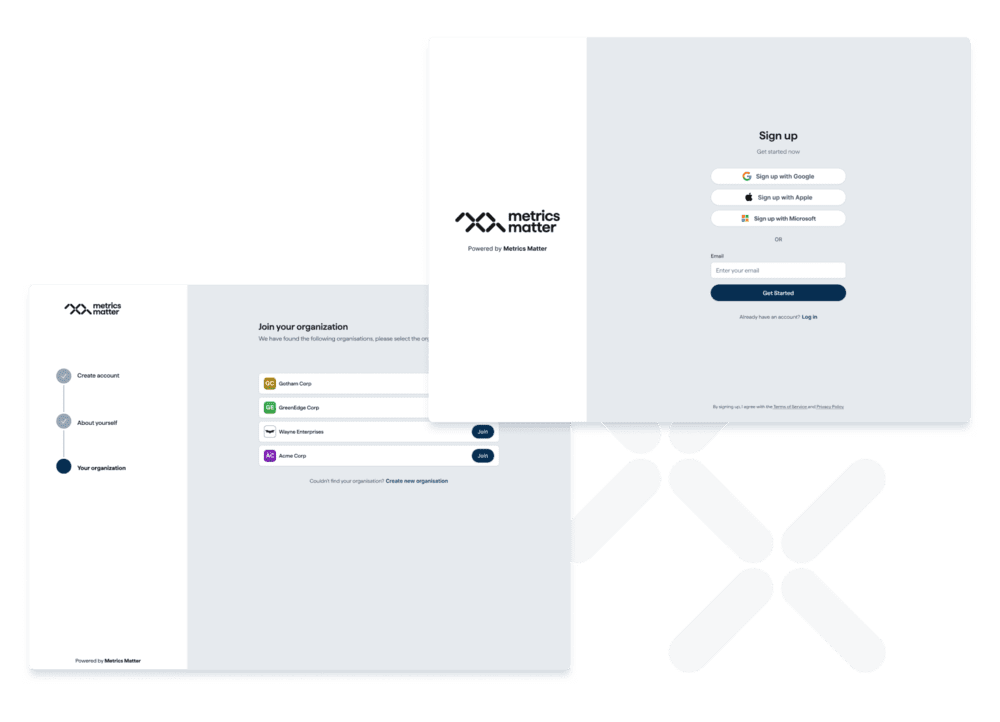
Onboarding
Our platform simplifies and streamlines the onboarding of new customers and organizations on your behalf, reducing friction and improving conversion rates. This is achieved through an intuitive self-serve process that guides users seamlessly from their initial interactions with your services to successful onboarding. By providing a user-friendly experience, we enhance the likelihood of customers committing to your offerings. Our solution not only saves time but also boosts the efficiency and effectiveness of the onboarding process, ultimately contributing to your business's growth and success.
Identity Management
Empower your organization to efficiently and comprehensively manage every aspect of the user identity lifecycle. This means from the moment a user joins your organization to their ongoing access and role changes, and finally to the secure and appropriate deactivation of their account when they depart.
Our solution provides you with the tools and processes to ensure that user identities are maintained and governed in a manner that aligns with your organization's security, compliance, and operational requirements. By managing the complete identity lifecycle, you can enhance security, streamline access, and maintain control throughout each stage of the user's journey within your organization.
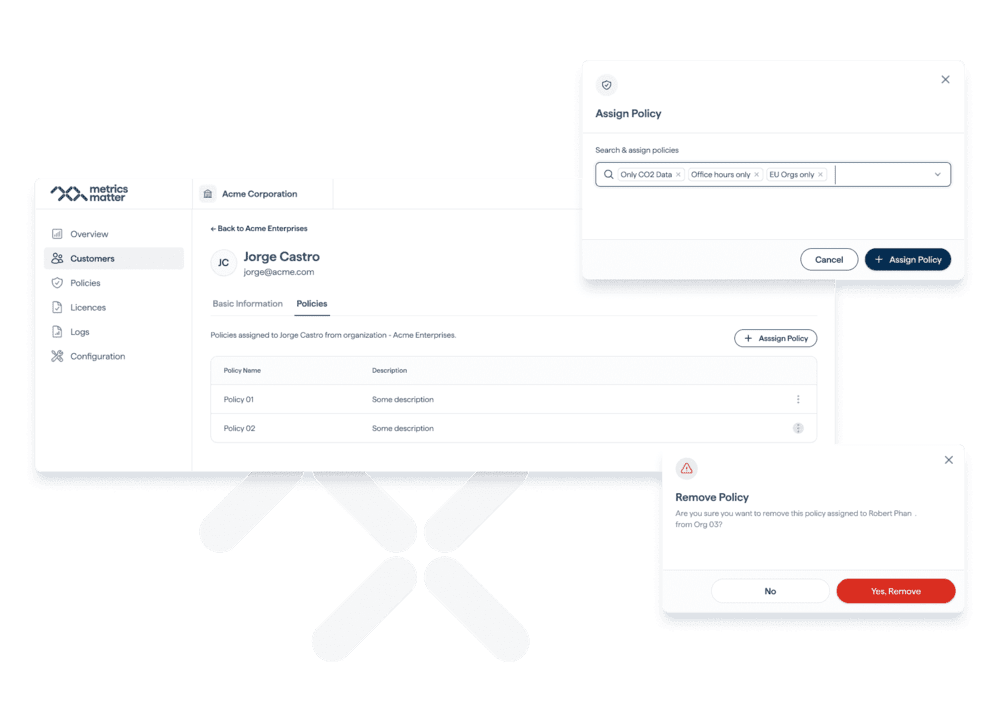
Access Management
Deliver a login experience that is both secure and user-friendly by selecting the right authorization method for your specific applications. Whether it's through username and password, single sign-on (SSO), biometrics, or other authentication methods, tailoring the authorization process enhances the security and convenience of user access. By making this choice, you not only protect sensitive data but also optimize the user experience, increasing user satisfaction and engagement. It's all about striking the perfect balance between security and ease of use.
Authentication
Enhance the user login experience by offering the flexibility to authenticate through various well-known and standard providers. This inclusive approach ensures a smooth and secure process for users, allowing them to choose from a range of trusted authentication methods. By accommodating diverse authentication providers, we create a user-friendly environment that aligns with user preferences and ensures data security. This flexibility not only simplifies the login process but also promotes user satisfaction and trust, ultimately leading to a more positive and secure user experience.
Frequently asked questions
Is there a free trial available?
At no cost to you, our fundamental services are available for use. This includes Onboarding, Customer Identity & Access Management system, and our Contracting and Compliance services – all at zero expense.
Is your solution limited in any way?
Rest assured, Metrics Matter's Customer Identity & Access Management solution has no restrictions. Feel free to add as many users, organizations, or units as you need without any surprises or limitations.
How can such an extensive solution be free of charge?
In our dedication to building a sustainable society, we provide all non-financial capabilities at no cost while maintaining a fully for-profit business model through our premium services.
When will Subscription Management be released?
This summer marks a significant milestone for our team and clients, as we gear up for the much-anticipated launch of our cutting-edge functionalities: Subscription Management, Contracting, and Compliance. This trio of enhancements is designed to revolutionize the way businesses manage their operations, offering unparalleled efficiency, security, and ease of use.
Is the beta release available for everyone?
The Beta version of CIAM is designed for real-world testing and is open to anyone willing to provide us with insightful feedback.